Cyber threats are evolving—can your business withstand an attack? Our penetration testing services simulate real-world cyber-attacks to identify security gaps, strengthen defenses, and ensure compliance with industry standards.
🔹Tiered Approach – Progress through vulnerability scans and in-depth assessments.
🔹Real-World Attack Simulation – Identify hidden weaknesses with ethical hacking techniques.
🔹Vulnerability Scanning – Detect system flaws and weak points in your IT enironment.
🔹Compliance Assurance – Meet GDPR, ISO 27001, and other regulatory requirements.
🔹Detailed Reporting – Gain actionable insights to fortify your security posture.
🔹CREST Certification – Industry-leading assessments backed by global benchmarks.
🔹Customised Security Strategy – A tailored approach suited to your business needs.
🔹Expert Team – Work with skilled cybersecurity professionals specializing in ethical hacking.
🔹Improved Customer Confidence – Demonstrate commitment to security and earn client trut.
✅ Industry Expertise – Our cybersecurity specialists have years of experience in ethical hacking and penetration testing.
✅ CREST-Certified Assessments – We follow globally recognized security standards to ensure high-quality testing.
✅ Tailored Testing Approach – We customize every penetration test to align with your business’s specific risks and infrastructure.
✅ Compliance-Focused Solutions – Our tests help you meet GDPR, ISO 27001, and other regulatory requirements.
✅ Actionable Insights & Reporting – Receive detailed reports with step-by-step recommendations to strengthen your security.
✅ Ongoing Security Support – Beyond testing, we offer continuous security monitoring and advisory services.
Penetration testing is a controlled security assessment where ethical hackers simulate real-world cyber-attacks against your systems, applications, and networks. The objective is to identify vulnerabilities, misconfigurations, and weaknesses that could be exploited by malicious actors.
Unlike automated vulnerability scans, penetration testing involves skilled security professionals who:
Within a wider managed IT services framework, penetration testing supports cybersecurity, cloud solutions, data protection, and long-term IT consultancy by delivering clear visibility into your true risk exposure.
Cyber threats continue to evolve, targeting organisations of all sizes across the UK. Firewalls, antivirus tools, and cloud security controls are essential, but they are not enough on their own. Penetration testing proactively validates your security posture by safely testing how your systems would respond to a real attack.
As part of a comprehensive business IT support approach, penetration testing allows you to:
This proactive testing approach ensures your IT support service is focused on prevention, not just response.
Our penetration testing services are flexible and tailored to your IT environment, risk profile, and compliance requirements. Each test integrates seamlessly with your existing IT support and cybersecurity controls.
Network penetration testing assesses the security of your internal and external networks, including servers, firewalls, switches, and endpoints.
External testing evaluates how exposed your organisation is to internet-based attacks, while internal testing simulates threats from compromised devices or insider risks. This is essential for organisations managing hybrid workforces and complex IT infrastructure.
Web applications often store sensitive customer and business data, making them a prime target for attackers. Our web application penetration testing identifies vulnerabilities such as injection flaws, authentication weaknesses, and insecure session handling.
This service is particularly valuable for organisations delivering customer-facing platforms, portals, or SaaS solutions supported by cloud-based IT services.
Cloud platforms introduce shared responsibility models that many organisations misunderstand. Our cloud penetration testing assesses configurations, access controls, identity management, and exposed services across public and private cloud environments.
We support secure cloud solutions while aligning testing with provider policies to avoid disruption to live systems.
Mobile apps introduce unique security challenges, including insecure data storage, API vulnerabilities, and weak authentication mechanisms. Our testing covers both iOS and Android applications, ensuring data protection across devices used by staff and customers.
Wireless networks can provide attackers with an easy entry point if poorly secured. Wireless penetration testing evaluates encryption, access controls, and rogue access points within your premises.
This testing is essential for organisations with multiple locations, guest networks, or legacy wireless infrastructure.
Technology alone cannot protect against human error. Social engineering testing assesses how employees respond to phishing, pretexting, and other manipulation techniques.
As part of a holistic IT support service, this testing highlights training gaps and supports stronger security awareness programmes.
Black box testing simulates an external attacker with no prior knowledge of your systems. Testers receive minimal information, reflecting real-world threat scenarios.
This approach is ideal for assessing internet-facing systems and overall security exposure.
White box testing provides full access to system documentation, source code, and architecture diagrams. This allows for deep, comprehensive testing and is particularly effective for complex environments.
It supports secure software development and long-term IT consultancy initiatives.
Grey box testing strikes a balance between realism and depth. Testers receive limited information, such as user-level access, to simulate a compromised account.
This method reflects many real-world breaches and provides high-value insight into lateral movement risks.
When Your Organisation Needs a Penetration Test
Penetration testing should be carried out regularly and at key stages in your IT lifecycle. Common triggers include:
For organisations relying on professional IT support services, regular testing ensures security keeps pace with business growth.
Benefits of Penetration Testing
Penetration testing delivers tangible business value beyond technical findings.
Benefit | Business Impact |
Reduced breach risk | Lower likelihood of data loss and downtime |
Improved compliance | Supports ISO 27001, GDPR, and sector regulations |
Better security investment | Focus spending on real risks |
Increased stakeholder trust | Demonstrates due diligence |
Stronger IT resilience | Supports long-term IT strategy |
When integrated with managed IT services, penetration testing strengthens your overall security posture.
Common Security Vulnerabilities We Identify
Our testing frequently uncovers vulnerabilities that automated tools miss, including:
Each finding is prioritised based on real-world exploitability and business impact.
Our structured approach ensures consistent, reliable results that align with best-practice cybersecurity standards.
We define objectives, systems in scope, testing methods, and risk controls. Clear scoping ensures safe testing without business disruption.
Testers gather information about systems, domains, and services using passive and active techniques.
We identify potential weaknesses using specialist tools and manual validation to reduce false positives.
Systems, services, and trust relationships are mapped to identify attack paths.
Applications are analysed for logic flaws, input validation issues, and authentication weaknesses.
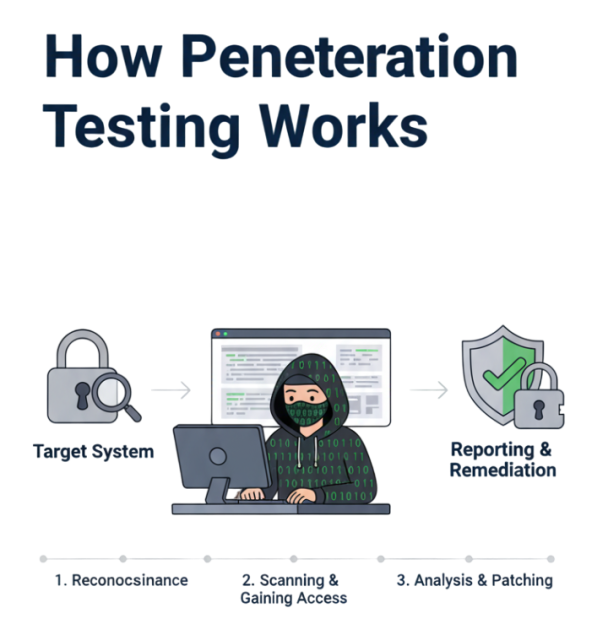
Validated vulnerabilities are safely exploited to demonstrate real-world impact.
We assess whether attackers could gain higher-level access within your environment.
Testers explore lateral movement opportunities across systems and networks.
Findings are documented in clear, business-focused reports, followed by a technical and executive debrief.
Our penetration testers hold respected industry certifications that demonstrate expertise and professionalism.
Recognised UK standard for penetration testing excellence.
Independent assurance of technical competence and ethical standards.
Certified Ethical Hacker credentials validating offensive security skills.
Advanced practical certifications demonstrating real-world testing expertise.
Governance, risk, and compliance expertise supporting strategic IT decision-making.

Penetration testing (pen testing) is a simulated cyber-attack designed to identify vulnerabilities in your IT systems before real attackers exploit them. It helps businesses strengthen security, ensure compliance, and protect sensitive data.
It’s recommended to conduct penetration testing at least once a year or whenever significant changes are made to your IT infrastructure, such as new system deployments, software updates, or security policy changes.
Vulnerability scanning automatically detects security flaws, while penetration testing goes deeper, using real-world attack techniques to actively exploit vulnerabilities and assess their impact.
Yes! Many regulations, including GDPR, ISO 27001, and PCI DSS, require businesses to perform regular penetration testing to maintain security compliance and avoid hefty fines.
The duration depends on the scope and complexity of the test, but most penetration testing engagements last between a few days to a couple of weeks. After testing, you’ll receive a detailed report with remediation steps.

Specifically designed for MSPs, software vendors, telecoms providers, and inhouse IT teams

© 2024 White Label Service Desk. A trading name of Creative Networks Limited. All Rights Reserved